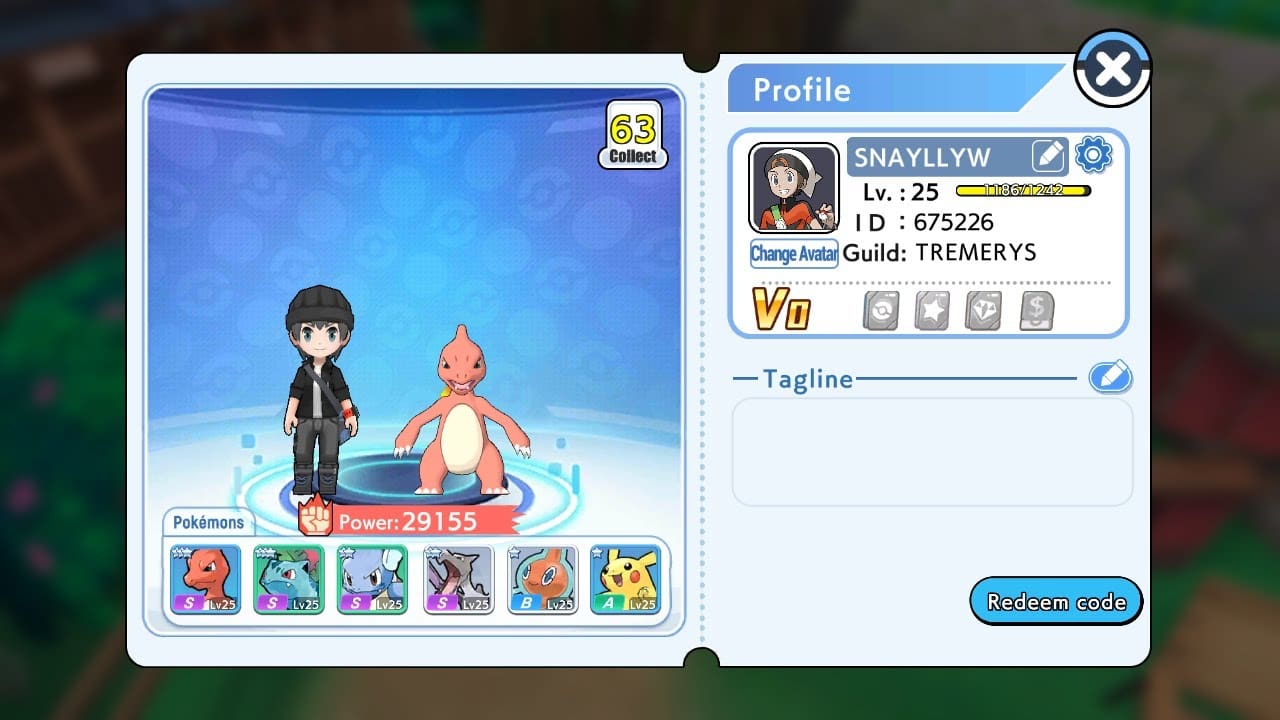
Gearup Booster Redeem Codes February 2024 – Easy Guide
February 7, 2024
Zerodha Clone App Redeem Codes February 2024 And Guide To Apply
February 7, 2024
MLBB EDOT.PH MLBB – Scan the QR Code and Redeem now
January 27, 2024
Skull And Bones Patch Notes 1.3
March 24, 2024
MapleStory Minar picnic GMS Patch with Bonus Event
March 24, 2024
Dragon’s Dogma 2 How to Unlock Magick Archer Vocation!
March 24, 2024




![Fix: Roblox Unable To Send Friend Request Error | Roblox Can't Send Friend Request 6 Bloxflip Promo Codes (February 2024) [Updated List!]](https://b3300814.smushcdn.com/3300814/wp-content/uploads/2023/10/Roblox-Bloxflip-Promo-Codes.jpg?lossy=2&strip=1&webp=1)







![MLBB Redeem Codes Today Update for February 2024 [Active] 15 Seal of Anvil Crawlers Patterns Mobile Legends Latest 2023](https://b3300814.smushcdn.com/3300814/wp-content/uploads/2023/09/Mobile_Legends_Bang_Bang_cover.webp?lossy=2&strip=1&webp=1)